Spam email delivery
Since Internet users and system administrators have deployed a vast array of techniques to block, filter, or otherwise banish spam from users' mailboxes and almost all Internet service providers forbid the use of their services to send spam or to operate spam-support services, special techniques are employed to deliver spam emails. Both commercial firms and volunteers run subscriber services dedicated to blocking or filtering spam.[1]
Webmail
A common practice of spammers is to create accounts on free webmail services, such as Hotmail, to send spam or to receive e-mailed responses from potential customers. Because of the amount of mail sent by spammers, they require several e-mail accounts, and use web bots to automate the creation of these accounts.
In an effort to cut down on this abuse, many of these services have adopted a system called Captcha: users attempting to create a new account are presented with a graphic of a word, which uses a strange font, on a difficult to read background.[2] Humans are able to read these graphics, and are required to enter the word to complete the application for a new account, while computers are unable to get accurate readings of the words using standard OCR techniques. Blind users of captchas typically get an audio sample.
Spammers have, however, found a means of circumventing this measure. Reportedly, they have set up sites offering free pornography: to get access to the site, a user displays a graphic from one of these webmail sites, and must enter the word. Spammers can equip pornography-carrying emails (and any email type in general) to enter searches into the search engine so a larger number of windows can be opened. For example, by simply inputting the word "porn" into Google's search engine, spam messages can open up several sites related to the word "porn." These messages make it very hard to trace the spammer as the search word(s) make it appear as if the spam receiver entered the word themselves. The search word will not appear in the recent searches and the windows will not appear in the History page unless a link is clicked on the site. Some porn-emails will link to specific sites and ask for the user to create an account and enter payment information. Once the user has successfully created the account, the user gains access to the pornographic material.[3] Furthermore, standard image processing techniques work well against many Captchas.[4]
Third-party computers
Early on, spammers discovered that if they sent large quantities of spam directly from their ISP accounts, recipients would complain and ISPs would shut their accounts down. Thus, one of the basic techniques of sending spam has become to send it from someone else's computer and network connection. By doing this, spammers protect themselves in several ways: they hide their tracks, get others' systems to do most of the work of delivering messages, and direct the efforts of investigators towards the other systems rather than the spammers themselves. Spammers may equip messages so they put in selected searches in search engines (I.E. Google) to open a greater amount of search windows. As long as the server's computer is open and on, the range of windows can increase. The increasing broadband usage gave rise to a great number of computers that are online as long as they are turned on, and whose owners do not always take steps to protect them from malware. A botnet consisting of several hundred compromised machines can effortlessly churn out millions of messages per day. This also complicates the tracing of spammers.
Open relays
In the 1990s, the most common way spammers did this was to use open mail relays. An open relay is an MTA, or mail server, which is configured to pass along messages sent to it from any location, to any recipient. In the original SMTP mail architecture, this was the default behavior: a user could send mail to practically any mail server, which would pass it along towards the intended recipient's mail server.[5]
The standard was written in an era before spamming when there were few hosts on the internet, and those on the internet abided by a certain level of conduct. While this cooperative, open approach was useful in ensuring that mail was delivered, it was vulnerable to abuse by spammers. Spammers could forward batches of spam through open relays, leaving the job of delivering the messages up to the relays.
In response, mail system administrators concerned about spam began to demand that other mail operators configure MTAs to cease being open relays. The first DNSBLs, such as MAPS RBL and the now-defunct ORBS, aimed chiefly at allowing mail sites to refuse mail from known open relays. By 2003 less than 1% of corporate mail servers were available as open relays, down from 91% in 1997.[6]
Open proxies
Within a few years, open relays became rare and spammers resorted to other tactics, most prominently the use of open proxies. A proxy is a network service for making indirect connections to other network services. The client connects to the proxy and instructs it to connect to a server. The server perceives an incoming connection from the proxy, not the original client. Proxies have many purposes, including Web-page caching, protection of privacy, filtering of Web content, and selectively bypassing firewalls.[7]
An open proxy is one which will create connections for any client to any server, without authentication. Like open relays, open proxies were once relatively common, as many administrators did not see a need to restrict access to them.
A spammer can direct an open proxy to connect to a mail server, and send spam through it. The mail server logs a connection from the proxy—not the spammer's own computer. This provides an even greater degree of concealment for the spammer than an open relay, since most relays log the client address in the headers of messages they pass.[8] Open proxies have also been used to conceal the sources of attacks against other services besides mail, such as Web sites or IRC servers. As spam from proxies and other "spammable" resources grew, DNSBL operators started listing their IP addresses, as well as open relays.
Web scripts
Besides relays and proxies, spammers have used other insecure services to send spam. One example is FormMail.pl, a CGI script to allow Web-site users to send e-mail feedback from an HTML form.[9] Several versions of this program, and others like it, allowed the user to redirect e-mail to arbitrary addresses. Spam sent through open FormMail scripts is frequently marked by the program's characteristic opening line: "Below is the result of your feedback form."
The ‘tell a friend about this page’ features some websites offer may be vulnerable by design in that they allow the visitor to add their message to the email that is sent. Consequently, such scripts are often abused to send spam, particularly so-called 419 scams.[10]
Spammer viruses
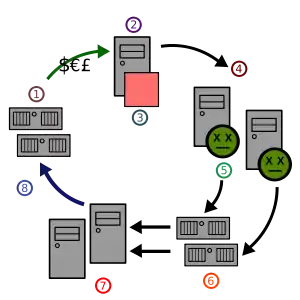
In 2003, spam investigators saw a radical change in the way spammers sent spam. Rather than searching the global network for exploitable services such as open relays and proxies, spammers began creating "services" of their own. By commissioning computer viruses designed to deploy proxies and other spam-sending tools, spammers could harness hundreds of thousands of end-user computers. The widespread change from Windows 9x to Windows XP for many home computers, which started in early 2002 and was well under way by 2003, greatly accelerated the use of home computers to act as remotely controlled spam proxies. The original version of Windows XP as well as XP-SP1 had several major vulnerabilities that allowed the machines to be compromised over a network connection without requiring actions on the part of the user or owner.[11]
Most of the major Windows e-mail viruses of 2003, including the Sobig and Mimail virus families, functioned as spammer viruses: viruses designed expressly to make infected computers available as spamming tools.[12][13]
Besides sending spam, spammer viruses serve spammers in other ways. Beginning in July 2003, spammers started using some of these same viruses to perpetrate distributed denial-of-service (DDoS) attacks upon DNSBLs and other anti-spam resources.[14] Although this was by no means the first time that illegal attacks have been used against anti-spam sites, it was perhaps the first wave of effective attacks.
In August of that year, engineering company Osirusoft ceased providing DNSBL mirrors of the SPEWS and other blocklists, after several days of unceasing attack from virus-infected hosts.[15] The very next month, DNSBL operator Monkeys.com succumbed to the attacks as well.[16] Other DNSBL operators, such as Spamhaus, have deployed global mirroring and other anti-DDoS methods to resist these attacks.
Zombie networks are particularly active in North America where about half of the Internet users are on a broadband connection and many leave their computers on all the time. In January, 2008, 8% of all e-mail spam was sent by the Storm botnet, created by the Storm Worm, first released in January, 2007.[17] It is estimated that as many as 1 million or more computers have been infected and their owners are unwilling and unknowing participants. In the 3rd quarter of 2008 almost one in every 400 email messages contained a dangerous attachment, designed to infect the recipient’s computer, eight times as often as in the previous quarter.[18]
References
- Proof of Work can Work
- Mori, G.; Malik, J. (2003). "Recognizing objects in adversarial clutter: breaking a visual CAPTCHA". Computer Society Conference: I-134–I-141. doi:10.1109/CVPR.2003.1211347. ISBN 0-7695-1900-8.
- Spammers turn to free porn to beat Hotmail security
- Using Machine Learning to Break Visual Human Interaction Proofs (HIPs)
- J Jung; E Sit (2004). "An empirical study of spam traffic and the use of DNS black lists". Proceedings of the 4th ACM SIGCOMM Conference.
- Open relay spam is ‘dying out’
- Securing Your Server: Shut the Door on Spam
- K Steding-Jessen; NL Vijaykumar; A Montes (2008). "Using low-interaction honeypots to study the abuse of open proxies to send spam" (PDF). INFOCOMP Journal of Computer Science.
- Wright, Matt (2002-04-19). "Matt's Script Archive: FormMail". Retrieved 2007-06-07.
-
"Abusable tell-a-friend scripts considered harmful". Retrieved 2017-04-05. Cite journal requires
|journal=(help) - Another Windows Bug Open To Zotob-Like Attacks
- Staff (2003-08-22). "Spammer blamed for SoBig.F virus". CNN. Retrieved 2007-01-06.
- Paul Roberts (2003-07-11). "New trojan peddles porn while you work". InfoWorld. Retrieved 2007-01-06.
- "Spammers Release Virus to Attack" (Press release). The Spamhaus Project Ltd. 2003-11-02. Retrieved 2007-01-06.
- Patrick Gray (2003-08-27). "Osirusoft 'closes doors' after crippling DDoS attacks". ZDNet Australia. Retrieved 2007-01-06.
- "Infinite Monkeys & Company: Now retired from spam fighting" (Blog) (Press release). DNSbl. 2003-09-22. Retrieved 2007-01-06.
- Don't fall in love with the Storm Trojan horse, advises Sophos retrieved 18 January 2008
- "Eight times more malicious email attachments spammed out in Q3 2008" (Press release). Sophos Plc. 2008-10-27. Retrieved 2008-11-02.